Gitora Enterprise comes with a comprehensive authorization module. Using this module, Gitora admins and other privileged users can assign various roles to Gitora users to limit or enhance what they can do during database development and using Gitora’s capabilities.
Authorization settings in Gitora can be set at three levels:
- Database
- Repo
- Database Object
Database Level Authorization
The highest level where privileges for users can be set is the database level. Only admins can set database level authorization. Each database managed by Gitora has its own authorization scheme that can be set separately.
Gitora Enterprise comes with two default roles: Developer and Release Manager. Customers can edit the database level authorization according to their needs by either editing existing default roles, deleting them or creating new ones.
Each user in Gitora Enterprise must be assigned a database level role.
Gitora provides database level privileges to execute the following functions. These priveleges can be given or taken from a role as desired:
System Privileges:
Edit Repos: Create, edit or delete repos.
Edit Remotes: Create, edit or delete remote repo entries.
Edit Repo Roles: Create, edit, delete or assign repo level roles.
Developer Privileges
Checkout: Take control of a database object to edit it.
Commit: Commit database objects to Git.
Edit Managed Schema Script: Edit the contents of the “Managed Schema Script” file in Gitora.
Repo Management Privileges
Add/Remove Objects: Add or remove database objects to/from a repo.
Add/Remove Schemas: Add or remove schemas to/from a repo for Gitora to keepo track of DDL statements executed in that schema.
Local Git Command Privileges
Reset: Execute the Git Reset command for a repo.
Create Branch: Execute the Git create branch command for a repo.
Change Branch: Change the active branch in the database for the repo.
Merge Branch: Perform a Git Merge for a repo.
Delete Branch: Delete a branch in a repo.
Tag: Mark a Git commit ID in a repo with a recognizable indentifier.
Remote Git Command Privileges
Push: Perform a Git Push to a remote repository.
Pull: Perform a Git Pull from a remote repo.
Fetch and Merge: Fetch a commit ID from a remote repo and merge it to the current branch.
Switch to Remote Branch: Fetch a remote branch and make it the active branch of the current repo.
Other Privileges
Get Script: Download the diff DDL script of two commit ID’s of a repo.
Rebuild from Working Directory: Execute the DDL statement file of a database object (or all database objects) in the working directory folder of a repo in the database.
Managing Database Level Authorization
Log in to Gitora as an admin. Select [Connected Database Name] – > Database Authorization menu item from the main menubar.
The Manage Database Roles page shows up.
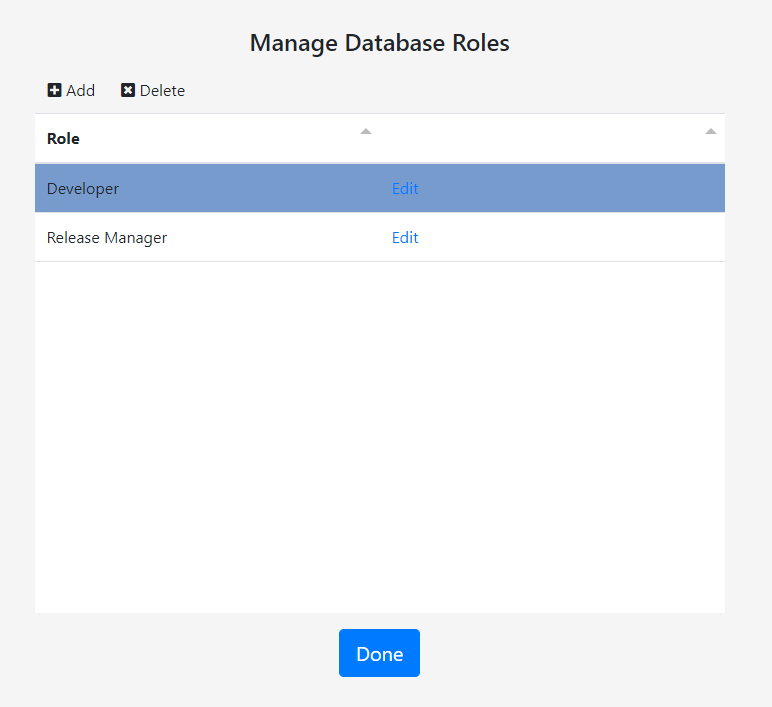
Gitora Enterprise comes with two built-in roles: Developer and Release Manager. Privileges for both of these roles are editable. You can also create your own roles.
To create a role click the Add button. The Create Role Dialog shows up. Enter a descriptive name for the role. Check the checkboxes next to the functions that you want the new role to be able to perform. Click the Save button.
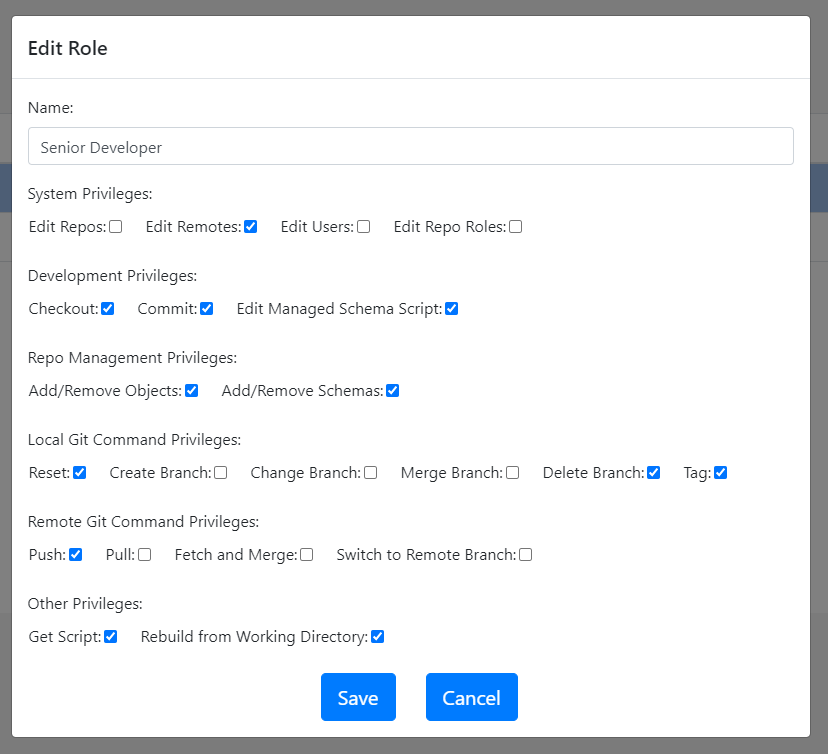
Editing existing roles work in a similar way.
Click the delete button on the Manage Database Role page to delete a role.
Repo Level Authorization
Repo level authorization is optional. An admin or a user with the database level privilege Edit Repo Roles can manage repo level privileges. When activated, repo level privileges override any privileges set at the database level for the database objects in the repo and Gitora functions performed for the repo. When users work with a database object that belongs to a repo with an active authorization scheme, they are assigned a repo level role that overrides their database level role. For example, a user with a database level Release Manager role, can act with a Developer role in the context of a repo with an authorization scheme of its own.
Once repo level authorization is activated for a repo, a repo level role must be given to a user explicitly. If no repo level role is assigned to a user, she will have no privileges in the context of the repo with repo level privileges. Admins are not affected by repo level authorization.
Repo level privileges that Gitora Enterprise provides are a subset of the database level privileges. System privileges are only set at the database level. The following privileges can be set at the repo level:
Developer Privileges
Checkout: Take control of a database object to edit it.
Commit: Commit database objects to Git.
Edit Managed Schema Script: Edit the contents of the “Managed Schema Script” file in Gitora.
Repo Management Privileges
Add/Remove Objects: Add or remove database objects to/from a repo.
Add/Remove Schemas: Add or remove schemas to/from a repo for Gitora to keepo track of DDL statements executed in that schema.
Local Git Command Privileges
Reset: Execute the Git Reset command for a repo.
Create Branch: Execute the Git create branch command for a repo.
Change Branch: Change the active branch in the database for the repo.
Merge Branch: Perform a Git Merge for a repo.
Delete Branch: Delete a branch in a repo.
Tag: Mark a Git commit ID in a repo with a recognizable indentifier.
Remote Git Command Privileges
Push: Perform a Git Push to a remote repository.
Pull: Perform a Git Pull from a remote repo.
Fetch and Merge: Fetch a commit ID from a remote repo and merge it to the current branch.
Switch to Remote Branch: Fetch a remote branch and make it the active branch of the current repo.
Other Privileges
Get Script: Download the diff DDL script of two commit ID’s of a repo.
Rebuild from Working Directory: Execute the DDL statement file of a database object (or all database objects) in the working directory folder of a repo in the database.
Managing Repo Level Authorization
Select a repo from the main select box in the Gitora Web App. Click the Git -> Repo -> Repo Authorization menu item from the menubar. The Manage Repo Roles page shows up.
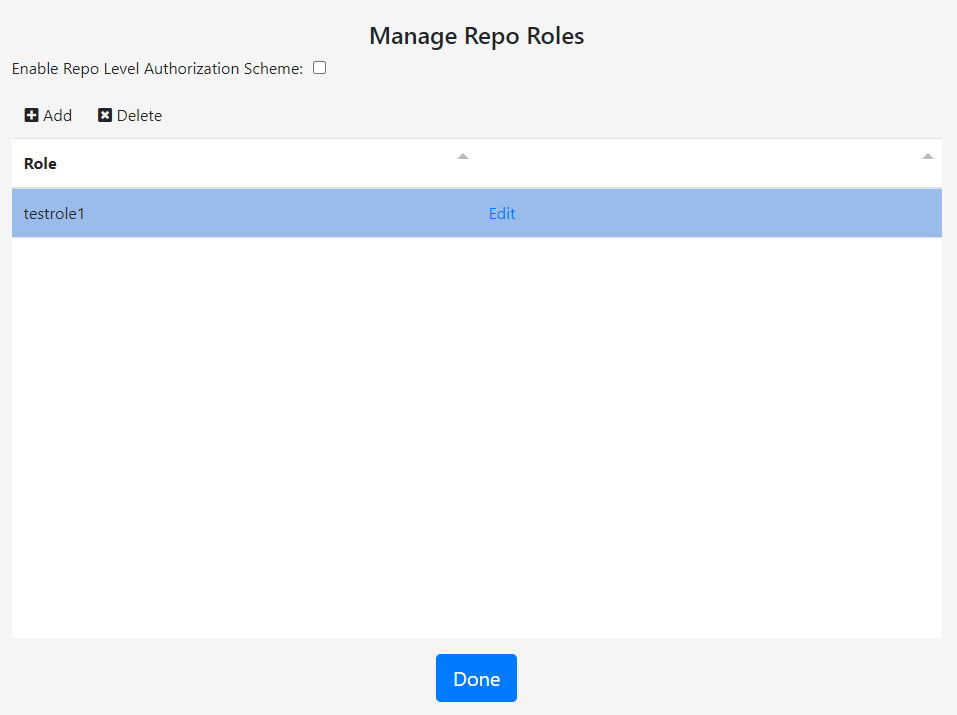
Use the Add, Delete and Edit buttons to manage repo level roles.
Check the Enable Repo Level Authorization Scheme checkbox so that the repo level roles take effect. You can disable repo level roles by unchecking this checkbox at any time.
To assign a repo level role to a user, click the [Connected Database Name] – > Users menu item from the menubar. Click the Edit button next to a user. The Edit User screen shows up.
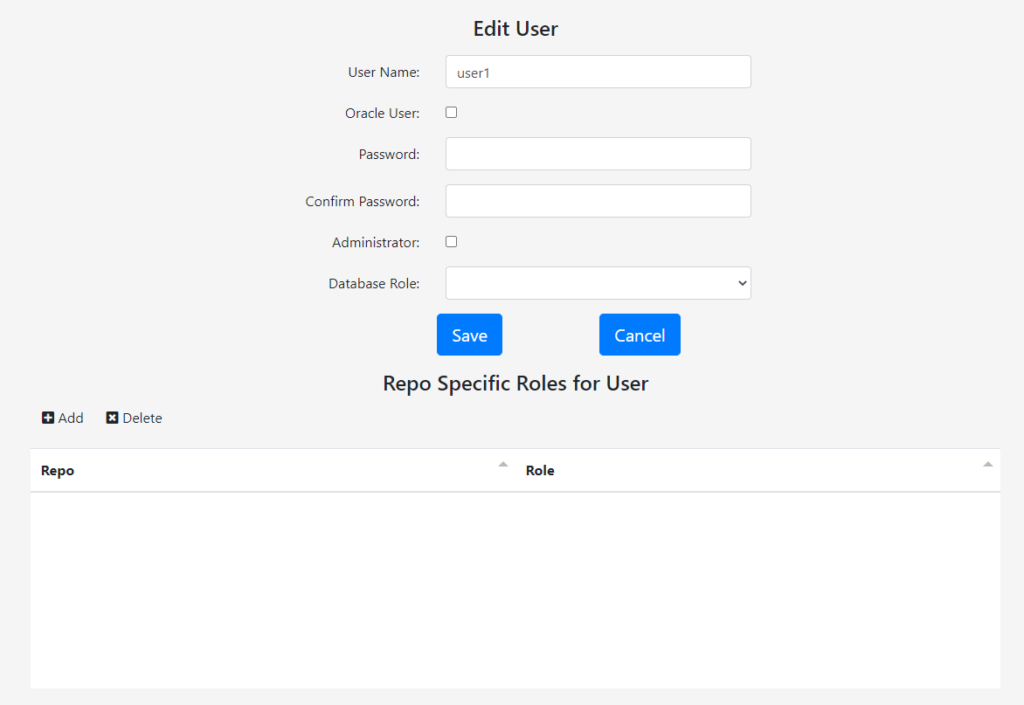
Please note that the top portion of this screen where you can edit a users name, password, database role etc… will only show up for admins.
The table at the bottom of the screen with the title Repo Specific Roles for User displays the roles a user has for a specific repo. To add a role click the Add button. The Add Repo Role Dialog shows up.
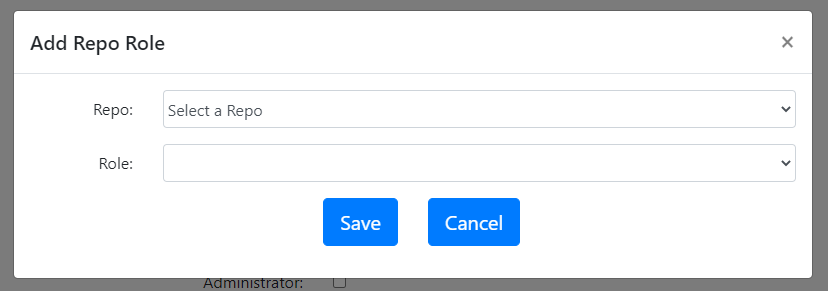
Select the repo and the role you’d like to assign to the user in this repo. Please note that the repo select box only shows repos with repo level roles. Click the Save button.
The assigned role will show up in the edit user page.
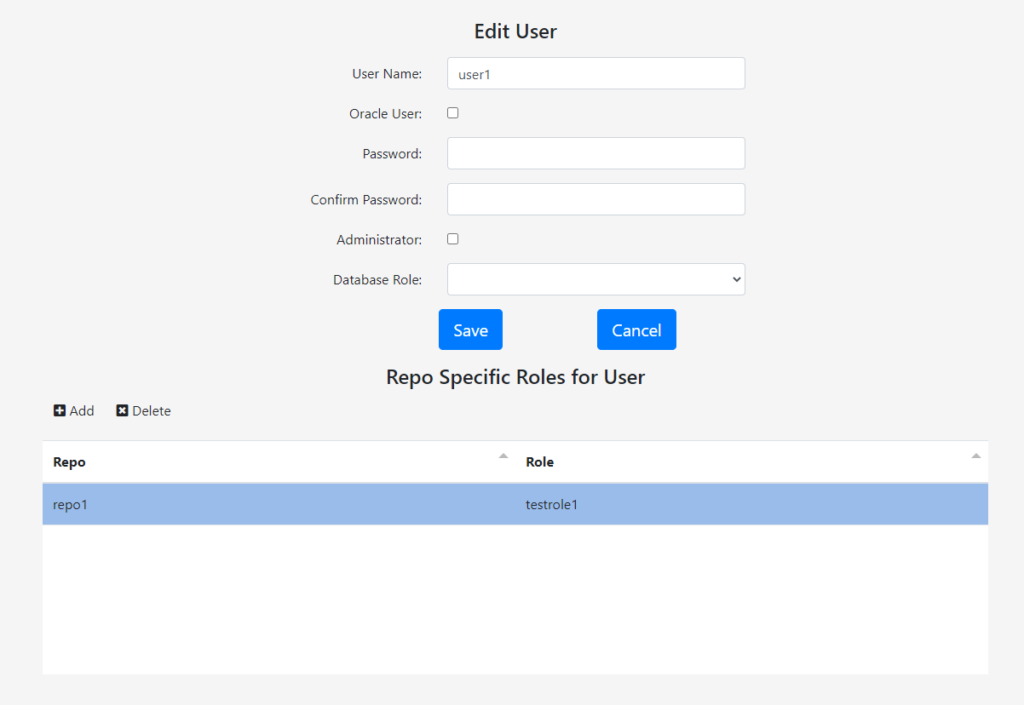
Please note that, a user can only have one role for a repo. To change the user’s role, delete the current role and create a new one.
Database Object Level Authorization
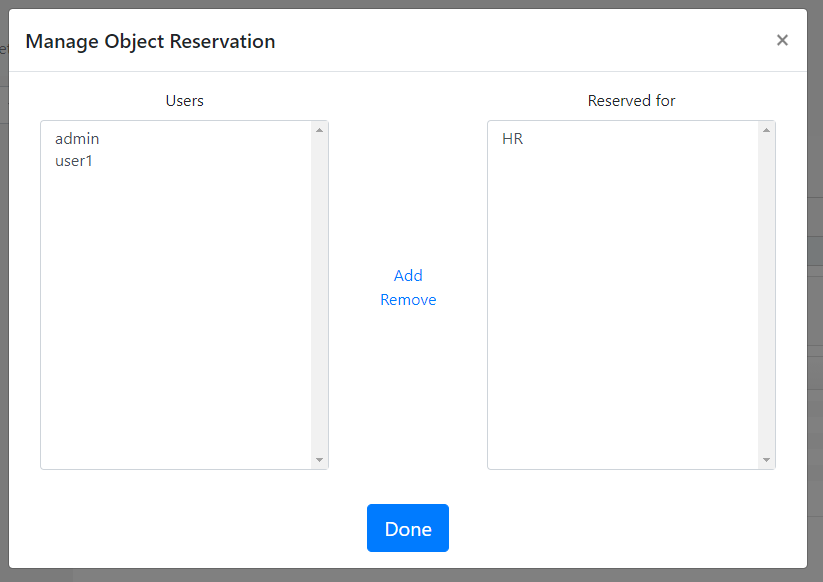
Gitora Enterprise enables admins and users with database level privilege Edit Repo Roles to reserve a database object for a user or group of users. This way, only the users in the reservation list can check out (and therefore edit) an object.
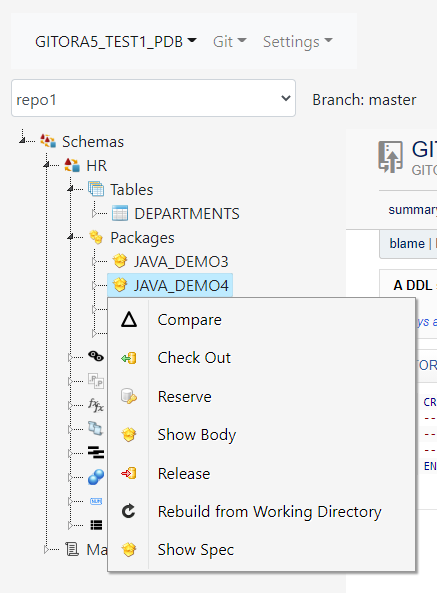
To achieve this, in the main select box, select the repo the obejct is in. Navigate to the object in the tree and right click to it. In the context menu, click Reserve.
The Manage Object Reservation Dialog shows up. Select the user and click the Add link to add the user to the list of users for whom this object is reserved. Click the Done button when you are finished.